The Threat is Real
Protect Yourself TODAY!

Protect Your Sensitive Law Firm and Client Information, Without the Hassle of Any Passwords.
Solve your cybersecurity concerns with a Hacker-Proof Way to Access all of your law firms’ key tools using one simple anti-[theft, phish, replay] code.
Maximize your client’s billable hours by entrusting ILogSafe to handle your security needs.
AN EXPERIENCED TEAM
With one Goal.
To Protect your Data
Your law firm stores incredibly valuable, sensitive information, and may even have a level of access to client trust accounts. This leaves your firm susceptible to theft and ransom, and makes you a ripe target for potential hackers.
➔ Ensure your protection today!
DON’T DELAY
THE THREAT IS REAL!

$4.47M
is the global average cost for a professional services data breach*

82%
of data breaches are due to human error*

65%
or 1 in every 2 law firms have been
The Threat is Real
PRESERVE YOUR PROFIT MARGINS WITH ILOGSAFE!

Safety and Access

Firm Success

Time-saving tool

Industry’s Highest Security Standard for Login Security (CJIS)
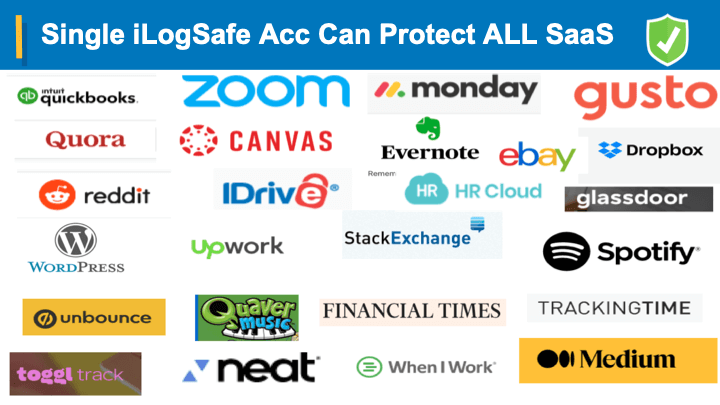
All of These Apps
NO PASSWORD NEEDED
ILogSafe works with the most popular apps used by law firms. Enjoy the comfort of knowing your client’s data is safe and the convenience of one code for all these apps without the headache of endless passwords and 2 factor authentication.
Testimonials
WHAT OUR CLIENTS ARE SAYING
Great experience with iLogSafe – NO passwords to deal with. I could test iLogSafe with a colleague in 30 secs that it is indeed useless for everyone else, except for me!

Bernard J. Rhodes
First Amendment Law
iLogSafe is now a part of my Law Practice as I am handling patents, trademarks and copyrights cases. Thanks to iLogSafe, I am free from headaches of multiple passwords. At the same time de-risk any of the unauthorized access to client documents could become prior art and severely impacting my clients in securing patents!

Dr. Nick Oberheiden
Attorney at Epiq Systems
iLogSafe made my life easier eliminating the risk of online hackers getting to my client-attorney privileged confidential documents. More over several of my financial accounts, billing and invoices tied together. Thanks to iLogSafe, I can now focus on my work and acquiring more clients confidently and securely.

Alan M. Rifkin
Attorney at Diaz and Associates
I used to think that there was no end to passwords and OTPs in my law practice. However, since I started using iLogSafe, my life has become much easier.

Michelle “Mika” Domingo
Estates & Trusts -California
easily protect your data
WITH ILOGSAFE

Prevent hackers from getting ahold of valuable client data.

No more passwords!

Avoid malpractice lawsuits and hikes in insurance premiums.

Access multiple online applications with one secure account.

Grow your client base with confidence!

Simple and fast setup!
Get Started Today!
Delaying to Start May Lead to Regret!

Get Exclusive Early Access
Need any help?
FREQUENTLY ASKED QUESTIONS
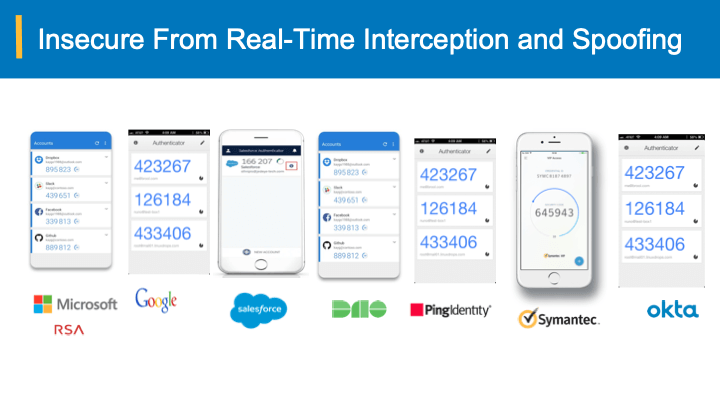
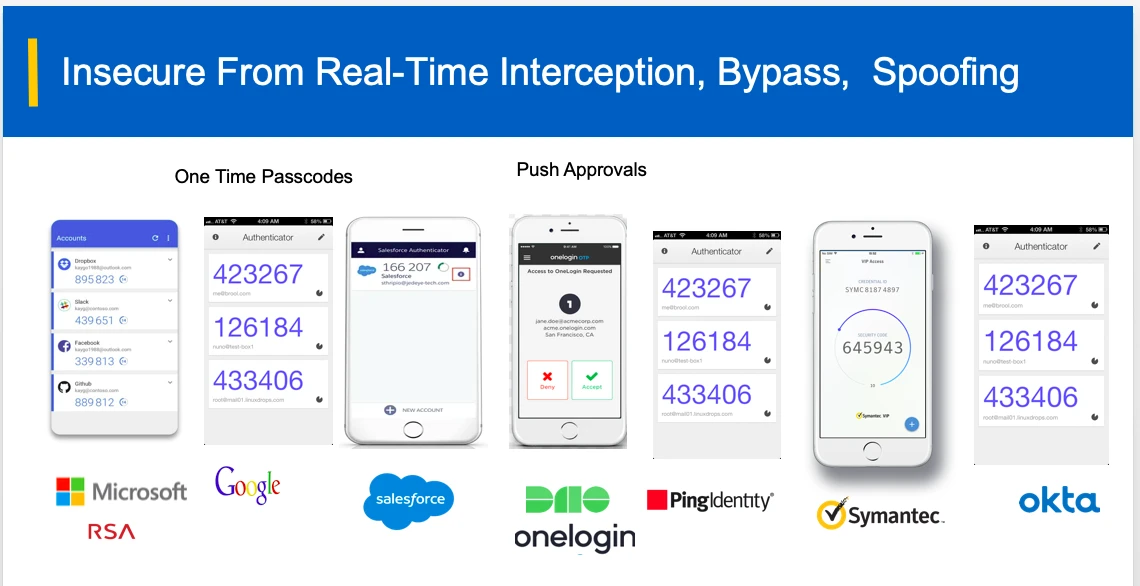
I use super strong passwords, One time codes, Push notification app approvals? Why do I need iLogSafe?
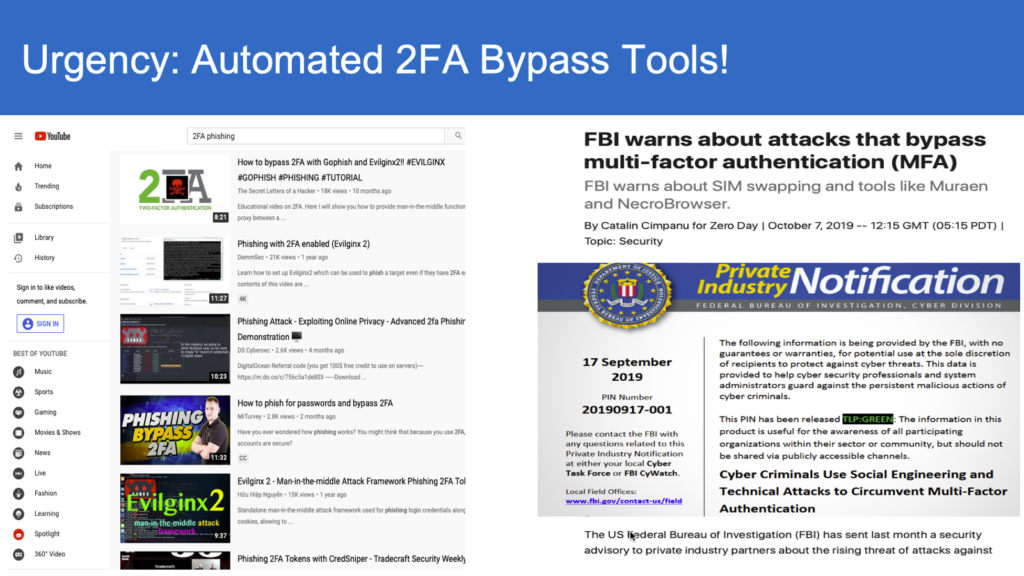
Can you show the details of how my 2FA is vulnerable(contains hacker demo videos)?
Below video demonstrates how push notification authentication/approval 2FA can be compromised.
Watch below video on how OTP 2FA can be compromised.
Disclaimer: *copyrights belong to breakdev.org
How does iLogSafe secure my online accounts, money from hackers?
If you are serious about securing your money and accounts from fraudsters, signup now for great early bird discounts (more than $150 value package)
I use faceId and Voice along with fingerprint and approvals on the app. Am I not secured?
Disclaimer: *copyrights belong to breakdev.org
I use public and private, aka- Passkeys; am I not secure?
Further, Passkeys are device specific. Syncing passkeys across devices is replicating passkeys across ALL the devices. Thus, every device from which you are logging in, need to carry same set of “secrets (aka passkeys)” translating into increasing attack surface. And one device compromise can expose all.
On the other hand iLogSafe lets you pick a backup device where you can keep and secure the backup secrets offline. However, NOT REQUIRED is to have secrets keychain replicated across ALL the devices that you want to login. Yet, for each device you can easily generate anti-phish anti-theft login codes thereby getting the MOST secure login from ALL THE DEVICES WITHOUT REPLICATING THE SECRETS ACROSS THEM UNLIKE PASSKEYS.
Further, your security is as good as securing multiple sync-up channels. With iLogSafe you are not required to connect to online or cloud for secret backups, but offline in your own privacy for backup. You CONTROL backup, not cloud providers! Biggest advantage is – you don’t have to uproot any other technologies including passwords etc but just tag on with iLogSafe anti-phish anti-theft anti-spoof technology out-of-box.

Reach us at
6275 W. Plano Parkway, Suite 500 Plano, TX 75093
© 2023 iLogSafe LLC. All Rights Reserved.
iLogSafe® reg. 6,764,547 USPTO